Double factor authentication,
its mandatory nature and poor implementation.
February 21st, 2022
There are more and more cyberattacks aimed at companies. Input factor: The human.
But... Are the users responsible for the protection of corporate data? Definitely not. Companies not only have a need to protect their systems, but also the legal obligation to protect their entire environment with the implementation of mechanisms that comply with data protection law, that restrict access to data by malicious users... in ultimately, that they are capable of guaranteeing a safe working environment.
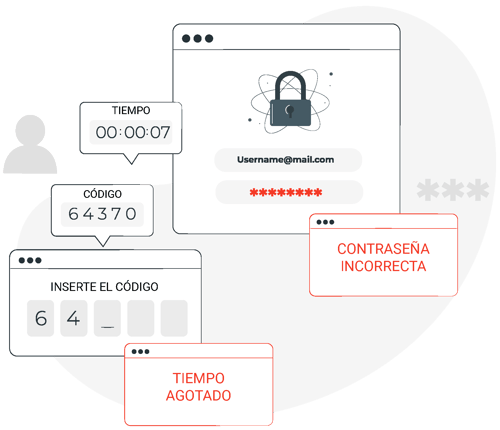
When we talk about security measures, passwords come to our mind inevitably, even reinforcement with OTP codes, or validation through messages for the most cautious... But given the increase in vulnerabilities in companies, it is evident that these obsolete methods do not comply with the necessary guarantees to ensure that the company's information is properly protected.
As much as companies emphasize over and over again the importance of generating strong passwords, most users will try to remember as few of them, and the simpler the better.
One of the great current problems is the lack of foresight that exists on the part of companies by not implementing new methods. In addition to being more and more latent and no matter how much old techniques are perfected and combined with the latest technologies, the factors that are analyzed are not enough to prevent these attacks.
For this reason, it is necessary to incorporate new layers that guarantee access security, and this is where the much-needed MFA comes into play, a system that private users are using more and more frequently but that has not yet been installed in the corporate sector. .
Why are companies reluctant to implement new MFA?
Companies are often afraid of implementing security measures that they consider will hamper the day-to-day activities of their employees and will generate more problems than already exist. Of course, using passwords, OTP codes... to authenticate is a "practical" system since they are known by the vast majority of people and avoid presentations of tools, instructions... and new implementation methods that distance companies from that "practicality".
But despite their easy use, these security factors are not a barrier to recurring cyberattacks and generate great vulnerabilities in companies that end up becoming a vector of entry for cyberattacks, affecting the company and causing production stops, great losses economic and reputational damage impossible to remedy in the short and medium term.
Most likely, part of this reluctance is also due to the lack of awareness of the existence of new authentication methods such as the Location-Based Identity Platform, something that should be solved with the awareness campaign to comply with the new Union data protection regulation. European (GDPR).
With the growing commitment to innovation in cybersecurity, also driven by the shift towards digitization of companies, methods have emerged that are easier to use than the best known, methods such as Ironchip's, easy to use and that truly add an additional layer of security. A layer of location-based security to prevent credential theft or leakage leading to theft of sensitive information or unauthorized access to the company's internal network.

At Ironchip we are committed to helping you not only to comply with these security regulations, but also to exponentially increase the security of your entire data network with our secure location-based security layer. A solution with the perfect balance between security and user experience, which above all helps to implement security measures in an easy and agile way for users' day-to-day activities without hindering them.
¿How does it work?
Our secure location technology is highly resistant to identity theft. This identity is generated based on behaviour patterns based on the users' locations. What does this mean? That each time a user accesses the Ironchip service, it learns in a transparent way from its location, generating an identity that helps to differentiate between legitimate users and malicious users.
All of this in a very simple way, through a management platform for the security administrator and a simple interaction through their mobile devices for the users.
But we know that many companies do not have a mobile fleet, so at Ironchip we have developed an implementation on desktop computers to facilitate the insertion of MFAs in work teams. You can also implement this innovative security layer without the need for users to validate access on their mobile devices, and doing so easily from their computers.
In addition, through our platform you can manage access and have visibility about what is happening in the company at the same time it is happening. Location-Based Identity Platform allows endless solutions to protect companies from improper access such as:
Además mediante nuestra plataforma podrás gestionar los accesos y tener una visibilidad de lo que sucede en la compañía en el mismo momento en el que sucede. Location-Based Identity Platform permite un sin fin de soluciones para proteger las empresas de accesos indebidos como:
- Protect and isolate backups,
- isolate and secure the different services from places only assigned to a location and denying all access that is not made from that place,
- access management based on the role played by each worker if desired.